Regarding the inspection of ongoing is CCleaner safe security incidents, we may wish to keep our customers and the overall staff informed of the latest findings. As disseminated in our past blog posts (here and here), the examination of the CnC server shows that the plot is an advanced persistent threat (APT) attack, mainly aimed at transparent cutting-edge and broadcast communication organizations. In other words, no matter is CCleaner safe the buyer’s product, the reason for the attack is not to attack the buyer and his information. Instead, CCleaner customers were used to accessing company systems with great achievements.
Today, we will reveal the new reality of that episode we have obtained since the last public update.
Table of Contents
Introduction
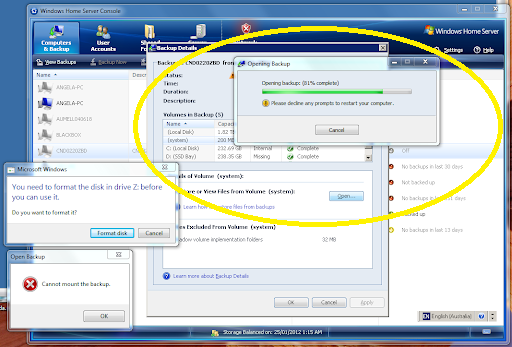
As we all know, in terms of the specific loss of the host transmitted by the CnC server and the failure of the host to which it sends the second-stage payload, the CnC server contains necessary evidence (for example, they can execute is CCleaner safe, harmful code assigned by the aggressor ). The problem is that due to an accident in the database, there are only about 3.5 days of information. Our theory was due to insufficient free space on the server on September 10.
prompting the administrator to recreate the database completely.
Nevertheless, further, inspection revealed that the attacker supported the information from the crushed CnC server to another server before modifying the database. Because the work of the Avast Threat Labs group has been carried out and has been assisted by personnel required by US law. The server’s IP address is 216.126.225.163, it contains a similar self-labeled SSL endorsement (the name of speccy.piriform.com), and has a standard “light” setting on the stack mode:
CentOS emissions 6.9 and Apache 2.2.15, PHP 5.3.3, especially the MySql database, finally contains the information is CCleaner safe returned to August 18. Accessing this hardened server allows us to collect the completed database (the central missing part is the 40-hour window between 2017) -09-10 19:03:18 and 2017-09-12 9:58:47 UTC, for example in Between is CCleaner safe the accident of the first CnC DB and the production of the enhanced version; for example, it is unclear how the CnC server was hosted during that period).
The principles found in the global database are as follows:
- The number of complete associations with the CnC server is 5,686,677.
- The total number of select PCs (except MAC addresses) is CCleaner safe communicating with the CnC server is 1,646,536.
- The total number of outstanding PCs that obtained the second-stage payload is 40.
- PCs and companies that received the second-stage payload
The most crucial piece of data is the content of the “correct” table in the database, which records the machines that effectively obtained is CCleaner safe the second stage payload and in this way were indeed “contaminated” by “possibly” harmful code is CCleaner safe (although the fact is that we have not yet Choose to isolate the system because it may originate from additional layers, and these additional layers are still the focus of other checks.
This is the final list of affected organizations/spaces, and the number of PCs affected is CCleaner safe:
We have established contacts with each of these organizations to provide them with precise data on the outbreak, the loss of affected PCs, and additional IOCs that can be used to identify contamination and take remedial is CCleaner safe measures.
The important thing is that among the 2.27 million PCs, about 40 PCs have introduced the implicit translation of CCleaner items; for example, 0.0018% of the total-really focused on attacks.
After some time, the consumption of the organization is CCleaner safe (space) has increased. The clear logs found on the SQL database server indicate that troublemakers are trying to identify reasonable hosts through predetermined consumption, but also investigate which PC has They can access them because they have a PC with CCleaner that interfaces with CnC.
The following is a summary of the highlights is CCleaner safe, which may be attractive, but have not been attacked by the second-stage payload:
These logs also indicate that the invaders are looking for new outstanding organizations to watch, some of which conceivably trigger more flexible chain attacks (operators/ISPs, organizations serving servers, and space recorders).
Strangely, when the CnC server was introduced, the two partnerships with the most significant number of affected PCs (cht.com.tw and nsl.ad.nec.co.jp) did not exist. Under. This shows that after delivering the payload, the invaders forcefully expelled these organizations from the endgame.
The starting point of the aggressor is CCleaner safe.
In the previous article, we discussed a variety of information indicating that this attack may have started in China, including many PHP code examples found on CnC servers, my PHP admin logs, and similarities to some code scraps. Past APT attacks have been attributed to China.
Along these lines of thinking, in our inspection process, we tried to adopt a unique marginal strategy. We see that there are usually a large number of administrator associations with CnC servers.
The server requires a lot of manual maintenance.
In total, the administrator has associated with the server multiple times (except for 17 additional hardenings of the server), from introducing and setting is CCleaner safe up the framework to observing the structure and solving individual problems (for example, repairing the attacked database). This makes us imagine that this is actually someone’s “normal daily work.”
Currently, with the establishment of this speculation, the significant activity is to draw the relationship between the administrator and the server in the diagram and try to determine the time zone where the attacker is located.
The result is cleaner safe, similar to:
There is a clear example, which is very common for IT workers: work 8 hours a day, sleep 4-5 hours at night/night, and then make new associations after 5 hours of blocking at night.
Given that the average working day starts at 8 a.m. or 9 a.m., this takes us to the most likely area of the attacker in the UTC+4 or UTC+5 time zone and takes us to the eastern part of Russia or the Middle East/Central Asia and India. In addition, due to poor traffic on Saturday and Sunday, this indicates that it is not an Arab country.
The important thing is that although there are a large number of technology/telecommunications organizations in China, Russia, and India, none of these countries have been paralyzed by this attack.
The examination process and subsequent stages are ccleaner safe
We are examining the incident: working with legal requirements. The partner organizations and expert companies, gaining practical experience in incident response activities, and acting quickly in the right way.
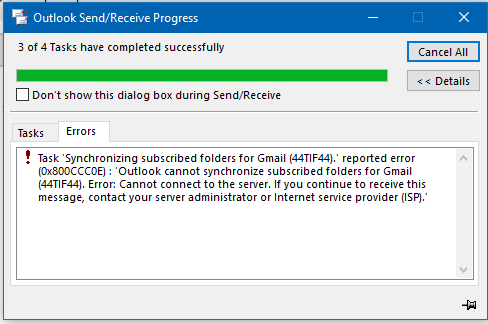
Obviously, the way the second-stage payload has been transmitted to the PC associated with the organization arrangement does not mean that the organization arrangement is destroyed. Nevertheless, proper inspections are all together and are important to fully understand the effects and take remedial measures. From our side, we have been working hard to gain access and check the extra stage (stage 2) of the payload. If other problems are found, we will post an update.
An update is CCleaner safe:
To the contaminated PC in an explicit way. And at least 20 computers in eight organizations reached the order and control server. The actual number of PCs that receive the second stage payload. It is likely to occur at any rate of hundreds of requests,” Avast said.
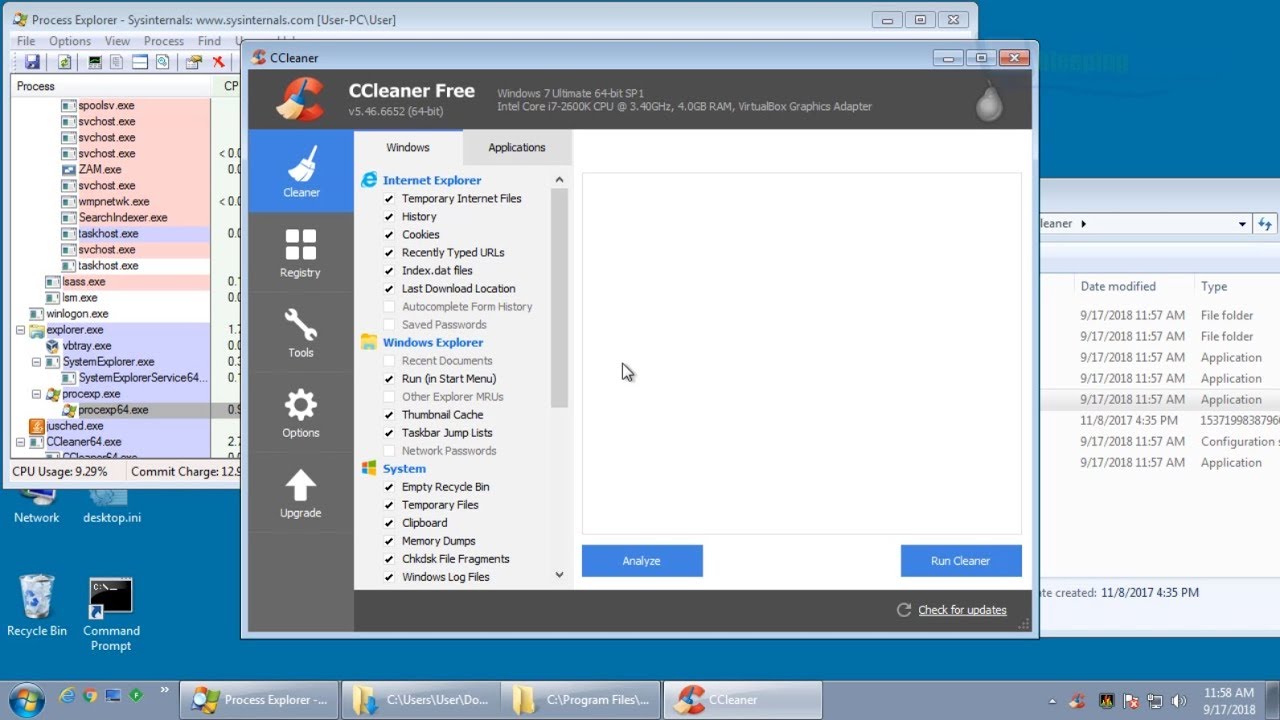
Cisco Talos also checked the ordering server for the malware. They were reported that it is working to infiltrate PCs in the Innovation Association. Including Intel, Samsung, HTC, VMWare, Cisco itself, and others. You can see the full summary on the right. Cisco Talos suspected that the attackers wanted to use the malware to lead modern secret work.
How to deal with CCleaner malware
If individual customers have not done so, they can download CCleaner 5.34 from Avast’s website. You also need to play antivirus filters on your PC. To the state before August 15, 2017, which is the release point of the hacked handover.
Impact on you at home:
Although each customer in the target area should not feel any impact from this hard attack, it is still a shocking idea. Smaller organizations may not be able to choose to respond so quickly, for example. Organization MeDoc was responsible for the NotPetya ransomware. Ransomware is becoming a disturbing pattern. Suppose programmers can contaminate update servers. They can spread malware to any number of computers that can be expected in this situation.
If you find it safe and helpless, please contact us; this is the ideal choice.
By providing secure items to ensure them and maintain their protection. It is ccleaner safe, this is our strategic protection for customers online. We constantly screen and test our framework. But we know that as a global programming is ccleaner safe organization. We will always be a well-known target for cyber criminals.
The run a reliable apocalypse program to provide rewards for anyone who finds or answers our projects. Sites or frameworks that are powerless. We will truly deal with all reports on security issues, and will thoroughly resolve the findings with you.
If you find any signs that cannot be defended in any is ccleaner safe of our frames. We urge you to illuminate us as soon as time permits. And do not disclose it remotely unless you do so. This is to ensure that we secure our customers by preventing malicious screen characters from taking advantage of this situation.
If it is not very troublesome, please report it is ccleaner safe as follows is ccleaner safe:
- Send an email to sec.report@ccleaner.com to report any signs that may lead to safety and helplessness to CCleaner. You can display this data secretly.
- Provide data about the discovery point by point (calculate accessible signs, such as IP addresses, logs, screenshots).
Unless we have taken steps to correct it, please do not publicly disclose data about defenselessness.
- When you report a weakness to us. We will respond within two working days. Work with you to assess the problem and determine the next stage.
- We will process your report in strict confidentiality. Without your explicit authorization, we will not pass any details of you to any outsider.
- When solving problems, we will continue to provide you is ccleaner safe with education about progress.
- With your consent, we will use your name is ccleaner safe. As a pioneer in this issue (if you don’t need us) to win honor for you. And you will be a delightful person in our programming field.
It is commendable that we will wholeheartedly express our gratitude to Avast for plundering or other ways. It is worthy of your decision based on the severity of the defect specified and the nature of your report.